Option Explicit
Private Declare Sub Sleep Lib "kernel32" (ByVal dwMilliseconds As Long)
Private Sub Form_Click()
Me.Caption = "Sleeping"
Call Sleep(20000)
Me.Caption = "Awake"
End Sub
Private Sub Label1_Click()
Me.Caption = "Sleeping"
Call Sleep(20000)
Me.Caption = "Awake"
End Sub
Taw dengan lagunya saykoji yang online? pasti pada taw kan? le pernah denger dia bilang wifi tapi binggung apa maksudnya?
mungkin dalam artikel ini lw bisa mengerti apa itu WIFI Artikel ini gw ambil dari basicvista25.blogspot.com mungkin artikel nya seperti ini
Wi-Fi (Wireless Fidelity) adalah koneksi tanpa kabel dimana kita tidak perlu menggunakan kabel pada pemasangan setiap perangkatnya. Wi-Fi memiliki kemampuan untuk menggerakkan perangkatnya tanpa memindahkan kabel atau perangkat lain dan tetap terkoneksi pada area layanan yang lebih luas (pada 3G). Wi-Fi juga menawarkan pelayanan data yang luas dan cepat (broadband) serta bandwith yang besar untuk memberikan pelayanan seperti realtime voice, data, dan streaming media. Pelayanan dapat diberikan secara terus-menerus tanpa henti (always on). Biaya yang dikeluarkan untuk mendapatkan Wi-Fi cukup rendah karena infrastruktur dapat dimiliki siapa saja dan tidak memerlukan lisensi. Selain digunakan untuk mengakses internet, Wi-Fi juga dapat digunakan untuk membuat jaringan tanpa kabel di perusahaan. Karena itu banyak orang mengasosiasikan Wi-Fi dengan “Kebebasan” karena teknologi Wi-Fi memberikan kebebasan kepada pemakainya untuk mengakses internet atau mentransfer data dari ruang meeting, kamar hotel, kampus, dan café-café yang bertanda “Wi-Fi Hot Spot”. Satu lagi kelebihan dari Wi-Fi adalah yang beberapa kali lebih cepat dari modem kabel yang tercepat. Jadi pemakai Wi-Fi tidak lagi harus berada di dalam ruang kantor untuk bekerja. Seperti halnya handphone yang menggunakan teknologi radio, pemakainya dapat mentransfer data dengan cepat dan aman. Dibandingkan dengan teknologi lainnya, Wi-Fi lebih mudah diterapkan oleh siapa saja dan di mana saja, sehingga setiap perusahaan atau perorangan dapat mengimplementasikan Wi-Fi di lingkungan mereka.
Sekilas Tentang WiFi
Dalam dunia industri Wi-Fi dikenal dengan teknologi komunikasi Wireless Local Area Networks (WLAN) yang berhubungan dengan standar jaringan nirkabel Institute of Electrical and Electronics Engineers (IEEE) 802.11. Wi-Fi merupakan teknologi yang memungkinkan sebuah komputer saling bertukar data secara nirkabel/tanpa kabel dalam suatu jaringan, baik intranet maupun berbagi akses internet. Wi-Fi dapat dioperasikan oleh internet provider atau individu. Wi-Fi bekerja pada protokol 802.11b dan 802.11g dengan transmisi standar 2,4 GHz, dengan kecepatan transfer data hingga 11 MB/detik. Versi 802.11a merupakan versi lanjutan yang beroperasi pada frekuensi 5 GHz dengan kecepatan transfer data hingga 54 MB/detik. Sedangkan 802.11g adalah campuran dari versi sebelumnya yaitu versi a dan b yang beroperasi pada frekuensi 2.4 GHz akan tetapi mempunyai kecepatan transfer data hingga 54MB/detik. Wi-Fi menggunakan teknik pengkode-an yang lebih efisien, sehingga memberikan kontribusi lebih untuk transmisi kecepatan data tinggi. Pada protokol 802.11a dan 802.11g menggunakan teknik orthogonal frequency–division multiplexing (OFDM).Sedangkan untuk protokol 802.11b menggunakan teknik Complementary Code Keying (CCK). Gelombang radio yang digunakan Wi-Fi memungkinkan untuk mengubah fre yang ada, bahkan bisa melakukan split pada bandwidth yang tersedia menjadi beberapa kanal dan frekuensi hop. Frekuensi hop digunakan untuk mencegah terjadinya interference (gangguan) ketika berada di antara pengguna Wi-Fi lain yang tengah mengakses secara bersamaan.
Manfaat Wi-Fi
Sebagaimana disampaikan diatas, Wireless Fidelity, atau biasa disingkat Wi-Fi, dapat membantu kita dalam mengakses dunia internet. Dunia internet dewasa ini telah terbukti dapat membantu beragam kegiatan manusia dimuka bumi. Karenanya dapat dibayangkan betapa nyamannya hidup ini jika bisa dengan leluasa mengakses internet hanya berbekal laptop, PDA atau smartphone, kapan pun dan di mana pun, tanpa direpotkan oleh kabel. Kita dapat mengakses internet di dalam mobil atau di toilet sekalipun. Peranti TI tersebut dapat menemani kita untuk “membunuh” rasa jenuh selama perjalanan jauh, dengan menyelesaikan pekerjaan selama perjalanan. Hasil pekerjaan dapat langsung dikirim ke kantor pusat tanpa harus mampir ke warnet atau wartel. Hal ini memberikan keuntungan dari segi waktu dan biaya. Jadi sisa waktu bisa dimanfaatkan untuk pekerjaan lain. Teknologi sekarang memungkinkan untuk itu. Wi-Fi diterapkan dengan layanan titik catu (hotspot) di beberapa tempat seperti di mal, kafe, bandara, hotel, kampus serta tempat yang berpotensi dalam pengumpulan massa. Hal ini dimungkinkan karena berkembangnya teknologi VoIP (Voice over Internet Protocol). Teknologi VoIP sendiri sebelumnya sempat membuat geger penyelenggara telekomunikasi yang tertinggal oleh pesatnya kemajuan teknologi telekomunikasi ini. Dengan jaringan Wi-Fi sangat dimungkinkan untuk melakukan hubungan ala VoIP atau ada yang menyebut dengan VoIP over Wi-Fi (VoWiFi). Teknologi in memungkinkan seseorang dapat berkomunikasi dengan mitranya di luar kota dengan biaya lokal atau bahkan gratis sama sekali melalui layanan Wi-Fi di cafe. Bahkan sekarang sudah ada handset untuk melakukan hubungan telepon VoIP melalui jaringan Wi-Fi, selain aplikasi telepon Push-to-Talk (PTT) melalui telepon VoIP. Pada jaringan telepon seluler produk handset PTT atau teknologinya juga disebut PTT over Celluler (PoC). Telepon video yang bukan hanya suara, tetapi juga gambar dari lawan bicara, merupakan peningkatan penggunaan VoIP over Wi-Fi. Kebanyakan perangkat yang dibuat masih untuk perangkat ponsel, dan penamaannya pun masih berbeda antar perangkat. Dengan PDA phone seseorang bisa bercengkerama melalui saluran Wi-Fi maupun jaringan telepon seluler sesuai dengan operator yang dilanggani, baik untuk berkomunikasi menggunakan gambar video atau hanya tulisan (chatting) atau bahkan hanya berbicara saja layaknya telepon konvensional atau HT. Belakangan ini, banyak perusahaan-perusahaan besar yang menggunakan jaringan Wi-Fi untuk memperluas jaringan kabel. Mereka menghubungkan titik akses nirkabel ke jaringan backbone mereka untuk menyediakan akses jaringan dan internet di ruang-ruang pertemuan, lobi, kantin, dan ruang-ruang umum lainnya. Tentunya ini akan memberikan fleksibilitas yang sangat tinggi, selain juga biaya yang murah. Komunikasi telepon nirkabel bisa dilakukan melalui Wi-Fi dan kita tidak perlu menggunakan saluran telepon atau koneksi internet lainnya selama masih berada di dalam jangkauan gelombang radio Wi-Fi.
Kelemahan Wi-Fi
Sebagai hasil produk teknologi, jaringan Wi-Fi bukanlah produk yang tidak memiliki kelemahan. Paparan mengenai kelemahan disini adalah bila dibandingkan dengan jaringan kabel. Kelemahan jaringan wireless secara umum dapat dibagi menjadi 2 jenis, yakni kelemahan pada konfigurasi dan kelemahan pada jenis enkripsi yang digunakan.kuensi. Card Wi-Fi 802.11b dapat melakukan transmisi secara langsung dari tiga band Salah satu contoh penyebab kelemahan pada konfigurasi adalah karena terlalu mudahnya membangun sebuah jaringan wireless. Banyak vendor yang menyediakan fasilitas yang memudahkan pengguna atau admin jaringan sehingga sering ditemukan wireless yang masih menggunakan konfigurasi wireless default bawaan vendor. Sering juga ditemukan wireless yang dipasang pada jaringan masih menggunakan setting default bawaan vendor seperti SSID, Ip Address, remote manajemen, DHCP, enable, kanal frekuensi, tanpa enkripsi bahkan user password untuk administrasi wireless tersebut. WEP (Wired Equivalent Privacy) yang menjadi standart keamanan wireless sebelumnya, saat ini dapat dengan mudah dipecahkan dengan berbagai tools yang tersedia gratis di internet. WPA-PSK dan LEAP yang dianggap menjadi solusi menggantikan WEP, saat ini juga sudah dapat dipecahkan dengan metode dictionary attack secara offlin. Sejak sekitar kuartal kedua 2005, Wi-Fi mendapat kompetitor dari WiMax yang masuk ke Indonesia. Tentunya disertai dengan teknologi yang lebih maju. Teknologi ini bekerja pada frekuensi 5.7 GHz. Dengan teknologi ini, transmisi data bisa berlangsung secara nirkabel antar perangkat yang terpisah pada jarak hampir 50 km. Teknologi Wi-Fi di Indonesia dalam hal pengaplikasiannya masih tergolong baru. Masih dijumpai kekurangan di sana-sini, bahkan kini akan menghadapi persaingan dengan teknologi yang lebih maju. Selain itu ada beberapa tambahan mengenai kelemahan dari Wi-Fi diantaranya : Kualitas pelayanan tidak ada barrier sehingga dimungkinkannya koneksi antar pengguna tetapi kualitas layanan kurang bagus contoh: suara. Pelayanan yang diberikan sedikit dan perkembangannya lambat Layanan suara pada Wi-Fi belum cukup sempurna dan masih banyak gangguan Tidak adanya barrier menyebabkan kemungkinan keamanan lebih rendah Wi-Fi tidak memiliki standar yang jelas dan masih menggunakan standar 802.11b yang masih dalam proses pengembangan lebih lanjut.
Sumber
1. Memblokir Remote Access => Utk mencegah PC anda diambil alih oleh Hacker,nonaktifkan Remote Access. Dlm menu Start, klik kanan pada “My Computer” & pilih “Properties”. Maka ada tampilan “System Properties”, kemudian pilih tab “Remote”, singkirkan/hilangkan tanda ( V ) yg ada didepan semua option yg ada utk menonaktifkannya. Kemudian klik “OK”.
2. Menghapus User Account yg tdk terpakai => Pada “Windows XP Professional” terdapat beberapa user account yg dapat diakses melalui trojan & dimanfaatkan utk melakukan penyerangan. Utk menyingkirkannya pilih menu Start, pilih “Control Panel”, pilih “Performance and Maintenance”. Kemudian pilih “Administrative Tools”, Klik 2 kali “Computer Management”. Pilih “Local Users and Groups”, pada sisi kanan klik 2 kali pd bagian “Users”. Hapuslah account2 lama yg tdk anda gunakan ( gambar users yg ada tanda X ). Kemudian tutuplah tampilan2 tadi.
3. Menutup celah NetBIOS => File2 dokumen anda bisa diakses melalui Internet maka nonaktifkanlah NetBIOS. Dlm menu Start, klik kanan pada “My Network Place” & pilih “Properties”. Maka ada tampilan “Network Connections”. Kemudian klik kanan icon koneksi internet yg tersedia, pilih “Properties”. Jika ada tampilan, pilih tab “Networking”. Beri tanda ( V ) yg ada didepan “Internet Protocol (TCP/IP), kemudian klik tab “Properties” yg ada dibawahnya. Maka ada tampilan “Internet Protocol (TCP/IP) Properties”, pilih tab “Advanced”. Tampilan ada lagi “Advaced TCP/IP Settings”, pilih tab “Wins”, lalu pilih “Disable NetBIOS over TCP/IP. Klik ‘OK”.
4. Penanggulangan terhadap BO2K pada Windows 9x => BO2K dapat dilacak dgn scanning port. Biasanya pd Windows 9x yg terbuka portnya hanya satu yaitu port 139 (NetBios). Oleh karena itu perlu dicurigai jika kita mengetahui ada port lain selain port 139 yg terbuka. Program anti virus yg beredar saat ini dapat mendeteksi keberadaan program ini. Pastikan anda sudah melakukan download versi terbaru dari program anti virus. Rajin2 lah membuka registrasi Windows. Biasanya pd Windows 9x, karena BO2K menanamkan dirinya pada
“HKEY_LOCAL_MACHINESoftwareMicrosoftWindows
CurrentVersionRunServices”
atau pada
“HKEY_LOCAL_MACHINESoftwareMicrosoftWindows
CurrentVersionRun”.
5. Pengamanan BIOS pada Server => BIOS merupakan perangkat lunak aras rendah yg berguna utk melakukan konfigurasi atau manipulasi hardware pada PC berbasis x86. MS Windows maupun Lilo dari Linux menggunakannya utk menentukan prosedur melakukan booting pada PC anda. Anda perlu memproteksi BIOS anda dgn memberi password padanya. Cara ini juga berguna utk mencegah penggunaan booting up melalui floppy disk. Cara ini tdk memberi perlindungan secara maksimal pada PC anda, namun dapat mempersulit org lain utk mengacak2 PC anda. Perlu diingat bahwa BIOS saat ini menggunakan metode flashroom, yg memungkinkan kita utk mengubah konfigurasi atau bahkan menghapusnya sama sekali.
6. Penyalahgunaan CGI Shell pada Unix/Linux => Ada beberapa cara yg cukup ampuh utk menanggulanginya :
a. Anda pasang Chrooted-Jail pada Apache anda sehingga perintah yg dapat dijalankan dapat anda batasi.
b. Utak-atik Source Code dari fasilitas CGI yg akan anda berikan misalnya Perl, kemudian anda matikan fasilitas fungsi system ( )… [Smile]
c. Minimalisasi terjadinya eksploit local pada sistem anda dgn sering mengutak-atik & mengikuti perkembangan berita seputar sekuriti.
7. Menghapus komponen COM yg tdk dibutuhkan pd Windows 2000/XP => Beberapa komponen COM yg tdk dibutuhkan oleh hamper semua aplikasi harus dihapus. Pertimbangkan dulu sebelum menghapusnya karena setiap komponen saling berhubungan dgn file system & dictionary object. Dalam menu Start pilih Internet Explorer, pada menu”Tools” pilih “Internet Options”. Jika ada tampilan, pilih tab “Connections”. Didalam “Dial-up and Virtual Private Network Setting” hapus COM yg tdk dibutuhkan dgn mengkliknya lalu pilih “Remove”. Kemudian klik “OK’.
8. Mengaktifkan Firewall => Agar Hacker & penyerang tidak sampai ke PC anda, dibutuhkan sebuah Firewall. Dengan Firewall, anda dapat memblokir beberapa port yg kerap diserang Hacker. Kami sarankan anda memakai McAfee Personal Firewall Plus 2004, McAfee Internet Security Suite 6.0 & ZoneAlarm.
9. Menginstalasi Anti Virus => Software antivirus tidak hanya menyingkirkan virus, worm, atau file perusak lainnya tetapi juga melindungi PC dari ancaman serangan Script di website. Kami sarankan anda memakai program antivirus McAfee VirusScan Professional 8.0, McAfee SpamKiller 5.0 & McAfee Worm Removal Plus.
10. Jangan anda melakukan chatting di MIRC sebelum tips diatas dipraktekkan, kalo tidak PC anda akan diseramg oleh Hacker karna IP anda bisa diliat melalui MIRC.
Sumber
VIVAnews - Owen Thor Walker, New Zealand hacker origin, be present as a cyber security consultant by TelstraClear, the second-largest telecommunications company in the country. TelstraClear is the son of Australia's largest telecommunications company, Telstra.
"We believe Walker has the ability to assist senior executives and customers understand the security threats that can attack their network," said TelstraClear spokesman Chris Mirams to the National Radio in Wellington, Wednesday 25 March 2009.
Years ago, Walker sued over data success penetrate 1.3 million computers around the world. Hacker by the name of this fictitious AKILL terbukti also damage the computer system and go through a number of bank accounts and steal more money from Rp 132.4 billion. At that time, the new Walker aged 18.
Not surprisingly, when he became the division incaran internet crime investigators from the Bureau of the United States (U.S.), FBI. The AKILL already meresahkan the penggun computer in the U.S. European
In front of the judge, the court in the city of Hamilton, New Zealand, he pleaded guilty on six criminal indictment internet. The judge at that time only impose penalties and fines to the Walker terpidana prohibit using the computer.
However, a group helping with the Walker pay fines and return the money so that they can claim on Walker revoked and youth is released.
Mirams said Walker had some counseling and providing advice to managers and security staff TelstraClear. Walker also participated in the program ad TelstraClear.
"Walker tells what are the cyber criminals and how to fortify their networks from threats that," said Mirams.
Some of the many hackers send electronic mail to the company's computer system or the government so that the excess capacity of the mailbox and enter the system.
Hacker techniques use other botnet, which is trying the computer and combine hundreds of computers in a kluster that have centralized control.
Then the hacker can use a combination of the computer to steal credit card information, manipulate stock trading, computer systems and destroy an industry. (AP)
> tukar
Click Here If U Wanna Be Sumber
VIVAnews - Owen Thor Walker, hacker asal Selandia Baru, kini dipekerjakan sebagai konsultan keamanan cyber oleh TelstraClear, perusahaan telekomunikasi terbesar kedua di negaranya. TelstraClear merupakan anak perusahaan telekomunikasi terbesar Australia, Telstra.
"Kami percaya Walker memiliki kemampuan untuk membantu eksekutif senior dan pelanggan memahami ancaman keamanan yang dapat menyerang jaringan mereka," kata juru bicara TelstraClear Chris Mirams kepada National Radio di Wellington, Rabu 25 Maret 2009.
Tahun lalu, Walker digugat atas kesuksesannya menembus data 1,3 juta komputer di seluruh dunia. Hacker dengan nama samaran AKILL ini juga terbukti merusak sistem komputer dan menerobos masuk sejumlah rekening perbankan dan menggondol dana lebih dari Rp 132,4 miliar. Saat itu, Walker baru berusia 18 tahun.
Tak heran, bila dia menjadi incaran petugas divisi kejahatan internet dari Biro Penyelidik Amerika Serikat (AS), FBI. Pasalnya, AKILL sudah meresahkan para penggun komputer di AS Eropa
Di depan hakim pengadilan di kota Hamilton, Selandia Baru, ia mengaku bersalah atas enam dakwaan kejahatan internet. Hakim saat itu hanya menjatuhkan hukuman denda kepada Walker dan melarang terpidana memakai komputer.
Namun, suatu kelompok membantu Walker dengan membayarkan denda dan mengembalikan uang yang mereka dapatkan sehingga tuntutan atas Walker dicabut dan pemuda ini dibebaskan.
Mirams mengatakan Walker telah mengadakan beberapa penyuluhan dan memberikan nasehat kepada staf pengelola dan keamanan TelstraClear. Walker juga ikut serta dalam program iklan TelstraClear.
"Walker memberitahu apa yang dikejar para penjahat cyber dan bagaimana membentengi jaringan mereka dari ancaman itu," kata Mirams.
Beberapa hacker mengirim banyak surat elektronik ke sistem komputer perusahaan atau pemerintah sehingga melebihi kapasitas kotak surat masuk dan menghancurkan sistem.
Hacker lainnya menggunakan teknik botnet, yaitu berusaha menguasai ratusan komputer dan menggabungkan komputer-komputer itu dalam sebuah kluster yang memiliki kontrol terpusat.
Kemudian para hacker dapat menggunakan gabungan komputer itu untuk mencuri informasi kartu kredit, memanipulasi perdagangan saham, dan menghancurkan sistem komputer sebuah industri. (AP)
* Jangan percaya otoriter/kemapanan - dukung desentralisasi.
* Hackers haruslah dinilai berdasarkan kemampuan hackingnya - bukannya berdasar kriteria seperti derajat, umur, ras, atau posisi. Anda bisa berkarya seni dan keindahan melalui komputer. Komputer dapat merubah hidupmu menuju kelebih baikan.
Sedangkan dalam prakteknya, Etika Hacker diatas (prinsip) dipraktekkan dengan mengikuti kode etik:
* Jangan merusak sistem manapun secara sengaja. (rmrf hard disk, crash, overflow, dll. Mengubah tampilan index.html sebuah website sah-sah saja asalkan file aslinya disimpan di sistem yang sama dan bisa diakses oleh administrator.)
* Jangan mengubah file-file sistem selain yang diperlukan untuk mengamankan identitas anda.
* Jangan meninggalkan nama asli anda (maupun orang lain), handle asli, maupun nomor telepon asli di sistem apapun yang anda akses secara ilegal. Mereka bisa dan akan melacak anda dari handle anda.
* Berhati-hatilah dalam berbagi informasi sensitif. Pemerintah akan menjadi semakin pintar. Secara umum, jika anda tidak mengenal siapa sebenarnya lawan bicara/chat kamu, berhati-hatilah!
* Jangan memulai dengan mentargetkan komputer-komputer milik pemerintah. Ya, ada banyak sistem milik pemerintah yang cukup aman untuk di-hack, namun resikonya lebih besar dari keuntungannya. Ingat, pemerintah punya dana yang tak terbatas dibanding dengan ISP/Perusahaan yang objektifnya adalah untuk mencari profit..
Sumber Artikel Klik Disini
* Access to computers - and anything which has the potential to teach you about this world to be free and total. All information should be freely available / free.
* Do not believe in authoritarian / kemapanan - to support decentralization.
* Hackers should be judged based on the ability hackingnya - not based on criteria such as degrees, age, race, or position. You can create art and beauty through the computer. Computers can change your life towards kelebih baikan.
While in practice, the Hacker Ethic (principle) practiced with the following code:
* Do not damage any system deliberately. (rmrf hard disk, crash, overflow, etc.. Change index.html a legitimate website, valid only as long as the original file stored in the same system and can be accessed by the administrator.)
* Do not change the file system other than that required to secure your identity.
* Do not leave the original name of your (and others), the original handle, and phone number in the original system that you access any illegally. They can and will track you from your handle.
* Be careful in sharing sensitive information. The Government will become smart. In general, if you do not know who the opponent actually talk / chat you, take care!
* Do not start with the target computers owned by the government. Yes, there are many state-owned system that is safe for the hack, but the risk is greater than the benefits. Remember, the government has unlimited funds, compared with the ISP / company objectives is to search for profit ..
Also known as 3l33t, 3l337, 31,337, or a combination thereof, is the spearhead of the network security industry. They understand sistemoperasi outside in, able to configure & connect the global network. Pemrogramman able to do each day. A grace that is very natural, they are usually effisien & adept, with the appropriate knowledge to use. Invisible as they can enter the system without the knowledge, although they will not destroy data. Because they always follow the rules.
Semi-Elite:
Hacker is usually more mudadaripada Elite.Mereka also have the ability & knowledge knowledgeable about computers. They understand the operating system (including lubangnya). Usually equipped with a number of kecilprogram enough to change the program eksploit. Many attacks are carried out by Hacker published this caliber, sialnya by the elite in their often picassoseven Categorize.
Developed Kiddie:
Appellative terutamakarena this age group is still young (ABG) & the school. They read about a method of hacking & how the various opportunities. They tried different systems to ultimately succeed & to proclaim victory lainnya.Umumnya they still use Graphic UserInterface (GUI) & learning new basic of UNIX, is able to find the hole without the weakness in the new operating system.
Script Kiddie:
As developed kiddie, Script Kiddie usually perform the above activities. As also Lamers, they only have the technical knowledge of networking is very minimal. Usually not separated from the GUI. Hacking is done using a trojan to frighten incommode & live in part of Internet users.
Picassoseven:
They are people without the experience & knowledge to become a Hacker (Hacker wanna-be). They usually read or hear about Hacker & want to like it. The use of their computers mainly to play the game, IRC, prirate exchange switch software, credit card theft. Like to use the hacking software trojan, nuke & DoS. Usually proud through IRC channels and so on. Because many kekurangannya to reach the elite, in their development will only be developed until the level or kiddie script kiddie course.
This Sumber
it has long nozzle - scratch, meaning ngepost ups. ok so first go I often have problems with MSDBGRID32 that cause I have to work 2 times, kok musti kerja 2 kali emangnya why? simple answer is I use a dbgrid connect it to ADO (data access object) nah happen after I setup the error message like this MSDBGRID32.ocx component not found, so I change into ADODC. For the friend - a friend with his problem with me please download component This Here
post I told about this time to encrypt part - 2 part 1 when encrypt it in this review to understand better the details, taken from a Wikipedia article is as follows:
In the field of cryptography, the encryption process is to secure the information by creating an information can not be read without the aid of special. Because encryption has been used to secure communications in various countries, only certain organizations and individuals that have a very urgent akan confidentiality using encryption. In the mid 1970s, strong encryption used by the secretariat for the security of the United States government agencies in the public domain, and at this time have been used in the encryption system widely, such as Internet e-commerce, mobile telephone network and ATM in the bank.
Encryption
In the field of cryptography, the encryption process is to secure the information by creating an information can not be read without the aid of special. Because encryption has been used to secure communications in various countries, only certain organizations and individuals that have a very urgent akan confidentiality using encryption. In the mid 1970s, strong encryption used by the secretariat for the security of the United States government agencies in the public domain, and at this time have been used in the encryption system widely, such as Internet e-commerce, mobile telephone network and ATM in the bank.
Encryption can be used for security purposes, but other techniques are still needed to make communications secure, particularly to ensure the integrity and authentication of a message. For example, Message Authentication Code (MAC) or digital signatures. Use the other is to protect the computer from the network analysis.
Contents
* 1 Ciphers
2 * Cipher code versus
* 3 Types cipher
Ciphers
A cipher is an algorithm to display the encryption and decryption of the, a series of steps that defined the procedure as follows. Alternative is encipherment. Information disebuh as the original plaintext and encrypted form which is referred to as chiphertext. Chipertext message contains all the information from the plaintext message, but not in a format that the computer or human readable without the use mekasnisme the right to do the decryption.
Cipher in the usually have the parameters of the main part of the information, referred to as the key. Encryption procedures vary widely depending on the key that will change the details of the operation algorithm. Without using the key, chiper can not be used for dienkirpsi or didekripsi.
Cipher versus code
In the non-technical usage, a secret code is the same as the cipher. Based on the technical discussions, however, code and cipher are described with two concepts. Work on code-level understanding, namely, the words or phrases changed to something else. Cipher, on the other hand, work on a lower level, namely, at the level of each letter, a group of letters, in the scheme of modern, in every bit. Some systems use both code and cipher in the same system, using superencipherment to improve security.
According to history, cryptography dikotomi into separate code and cipher, and the use of code has its own terminology, the same thing also happened in cipher: "encoding, codetext, decoding" and so forth. However, code has a variety of ways to be returned, including the fragility of the kriptoanalisis and difficulties to manage the list of code that is difficult. Therefore, the code is no longer used in modern cryptography, and cipher to become a more dominant technique.
Types cipher
Is a lot of variations on different types of encryption. Algorithm used in the early history of cryptography are very different from modern methods, and modern cipher and classified based on how the cipher is operating and cipher using a key or two.
Encryption Diagram
History Cipher pen and paper in the past tense is often referred to as classical cipher. Cipher cipher including classic and replacement cipher transposisi. In the early 20th century, the machines use a more up-to-date for the purposes of encryption, engine rotor, the beginning of the merupkan scheme more complex.
Encryption method is divided into key algorithm Symmetric and asymmetric key algorithms. Symmetric key algorithm on (eg, DES and AES), the sender and recipient must have a key that is used together and kept kerahasiaanya. Sender menggunkan key for encryption and the recipient uses the same key for decryption. In the asymmetric key algorithm (eg, RSA), there are two separate keys, a public key is published and to allow anyone to do the encryption the sender, while a private key kept by the recipient kerahasiannya and used to perform decryption.
Symmetric key cipher can be distinguished in two types, depending on how the cipher works on blocks of symbols at a fixed size (block ciphers), or the flow of ongoing symbols (stream ciphers).
From Wikipedia, the free encyclopedia
hallo vb ker wherever you are, it has been scrawled ech Reviews diblog mean, hehe. advised that it is rushing to leave and I have a problem with the doctor, hehe. so I will not have long - long may fuss you heard about encrypt and decrypt, but you do not know what the meaning of it to the 2. Ok I will try to translate what decrypt program is a system that has been made in exekutable which can not change back in the encrypt keblikan from the above, still binggung? ok may be a small example like this decrypt it when we eat or eat lemper previous lontong sure dah in gift-wrap? nah it is called decrypt, and encrypt the raw material is made before lemper or lontong such as rice, etc.. still binggung? ok for example I love coding that I take from VB6 is a master of the capture site http://www.masinosinaga.com, thank you pack it commandant info, and this example code: Code Program : 'Deskripsi: Mengencrypt/decrypt suatu file teks menjadi file teks yang |
Visual Basic Express The evolution of Visual Basic VB 1.0 introduced in 1991, I made the approach to connect with GUI programming language derived from the prototype I dikembang by "Alan Cooper" I call on the tripod,. Then Microsoft contract for copper and asosiasinya the tripod so that it can be used in Windows 3.0 under the code name Ruby. Next Travel Visual Basic (VB 1.0 VB To date, 10): Travel from Visual Basic (VB VB1 to 10) 1. Project "Thunder" dirintis 2. Visual Basic 1.0 (May 1991) on the release for windows on the Comdex / Windows Wordltrade I dipertunjukan in Atlanta, Georgia 3. Visual Basic 1.0 for DOS was released in September 1992. This language is not compatible with Visual Basic for Windows. VB 1.0 for DOS on kenyataaanya this is a continuation of the compiler version of BASIC, BASIC and QuickBasic Professional Development System VB For Dos 4. Visual Basic 2.0 was released in November 1992, coverage pemrogramannya quite easy to use and the speed also has been modified. Especially on the Form enacting the object can be made immediately, and the basic concept of Class I modules implemented in the next 4 VB 5. Visual Basic 3.0, released in summer 1993 and is divided into standard and professional versions. VB 3 Version 1.1 include Microsoft's Jet Database Engine you can read and write Jet database (or Access) 1.x 6. Visual Basic 4.0 (August 1995) is the first version of windows you can create 32 bit programs as well as its 16 bit version. VB 4 also introduced the ability to write non-GUI classes in Visual Basic 7. Visual Basic 5.0 (February 1997), Microsoft released Visual Basic exclusively for 32 bit version of windows. Programmer writer on the program's 16-bit version can easily do porgramnya import from VB4 to VB5. and also vice versa, VB5 program can be imported into VB4. VB 5 memperkenalakan ability to create a User Control. 8. Visual Basic 6.0 (mid 1998) to improve some of the coverage, temasuk kemapuannya to create Web-based applications. Visual Basic 6 will enter the schedule in Microsoft "Non-Supported phase" began in March 2008 9. Visual Basic. NET (VB 7), released in 2002, a few attempts in the first version. NET is revealed that the language is very powerful, but the language you use is very different from the language previously, with the shortage in different areas, including its runtime is 10 times greater than the VB6 runtime package and use the increased memory. 10. Visual Basic. NET 2003 (VB 7.1), released by using the NET framework version 1.1. 11. Visual Basic 2005 (VB 8.0), is the next Iterations of Visual Basic. NET. and Microsoft decided to remove the word word. NET in the title. Released on this, Microsoft bebrapa incorporate new features, including: 1. Edit and Continue, perhaps this is the lack of features of VB. NET. in VB 2005 allowed us to make changes to the code when the program is being executed 2. Improvement in the conversion of VB to VB NET12Visual Basic. NET 2003 (VB 7.1), released by using the NET framework version 1.1. 12. IsNot Patent, is one of the features of Visual Basic 2005 is a conversion If Not X Is Y into Y If X IsNot 13. Visual Basic 2005 Express, part of the Product merupkan Visual Studio. Microsoft makes Visual Studio 2005 Express edition for beginners and crazy with the VB, one of the product is Visual Basic 2005 Express is a product you free from Microsoft 14. Visual Basic "Orcas" (VB 9.0), is scheduled to released in 2007 and dibangung above. NET 3.5. On this release, Microsoft added some features, including: - True Tenary operator, the function If (boolean, value, value) I used to replace the IIF function - Support LINQ - Lambda expressions - XML Literals - Nullable types - Type Inference 15. Visual Basic 'VBx' (VB 10.0), Visual Basic 10, which also dkenal with VBx name, will offer support for the Dynamic Language Runtime. VB 10 is planned to become part of the Silverlight 1.1 |
Go directly to the discussion ...
1. Please list in http://www.700megs.com
why do I send you the list there?
in the web hosting is free and there is also support from the php in ripway.com
if not registered simply log in at:
http://www.700megs.com/register.jsp
2. after you successfully register the incoming 700megs.com FILE MANAGER to delete the file index.html .... (there will be later in the Cpanel masing2)
3. OK, we start our practice.
needed is the file index.php and write.php as the core fakelogin
scriptnya please download here or in the first
http://www.ziddu.com/download/5023245/scriptFakeloginFacebook.rar.html
free size 9kb.
4. after you download. There are two files called only index and write
both you please upload the 700megs.com before you have a list.
5. ago index.php first test I've uploaded and you log in from there,
I was successful .. there will be a new file; Password.txt [aim as the place where the UserID and password that will tertampung on facebook you fakelogin]
6, alright! finished up here. . .
for distribution please masing2 way ...
cm here I love to sample one taking by force account2 facebook mania ..
open the file in the index www.700megs.com URL you .. take it .. [important]
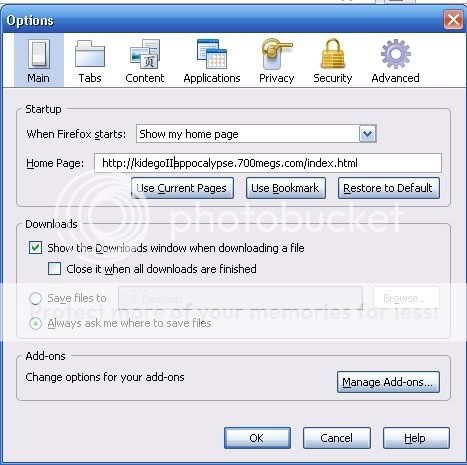
hold for firefox users: open tools> options> main
preview:
here we refer in order to function within the browser first opened the file directly led to us earlier. ravin allows you more later.
sebar to be in what the computer / in warnet2 favored.
or ..
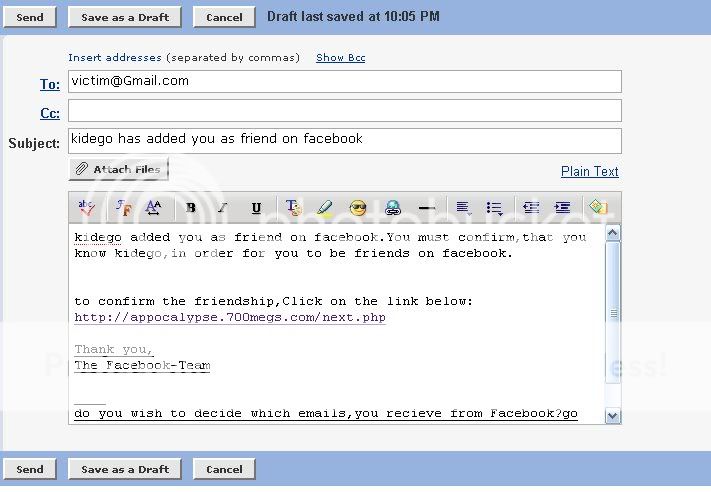
can also spread this way
you create a new account, in yahoo, gmail, like ato
with nick @ Facebook or something like that.
cm above example ... please make your own art
enjoy ..
easy?
hopefully successfully. . .
reference:
cyberdos forum, yogyafree, balikit
If you are looking for that unique personal gift that will make your chosen recipient smile, and is sure to be appreciated, a t-shirt with that funny joke or one liner on it or an amusing unusual picture or graphic is an ideal solution
Giving the gift of laughter in the form of a t-shirt can be seen in many different ways. You can use it to share a joke with your fellow human beings, or it can be enjoyed solely by the wearer of the t-shirt. They can be clean risque or just plain offensive, its your choice. Some rude ones are designed to shock the person who reads it, and the wearer of these type of humorous t-shirts has to be a certain type who enjoys the reaction this will get. When buying a funny t-shirt as a gift it is important to consider the personality of the intended recipient.
These garments can also make a social or political statement as well, they can deliver a message or an opinion, and are a great way of showing our personal identity. When one wears a funny t-shirt they are stating, "This is who I am and this is what I believe". Funny t-shirts are also a good way to break the ice in a social situation. Men and women no longer have to struggle with cheesy pick-up lines as they can simply state their interests on a funny tee.
They are as varied as you want them to be with inventive graphics or just a printed message , even if the t-shirt contains no graphics they can look very decorative with a unique and funny message emblazoned on the front for the whole world to see. With inventive design even plain prose with no graphical element can still be bright and attractive as there are thousands of fonts to liven up the words.
All-in-all, funny t-shirts are a great way to share laughter with your fellow man . You can cheer up any situation with a joke Just by wearing one yourself. Or buy them for friends or family as an ideal gift. its also an easy way to let people see your humorous side no matter how shy you may feel.
If you are looking for that unique funny t-shirt for yourself or a friend or relative take a look at http://www.naturally-stoned.com site. Their designs range from clean to risque, offensive or just funny, pictures or graphical images all designed by professional graphic designers and award winning photographers.
If you are of an artistic bent then why not make your own, at http://www.zazzle.com/naturally-stoned* . You can put your design on not only t-shirts, but a massive range of other personal gifts, including mugs, shoes, skateboards, figurines and many more, and if you are stuck for inspiration there are literally millions of designs that you can choose from.
gw binggung maw nulis ape, langsung aja y neh artikel gw dapet dari rum sebelah Bikin fake login tanpa banyak babibu lagi mungkin artikel ny seperti ini
Siapa sih yang tidak kenal Facebook di zaman yang serba internet ini ? Yap, Facebook adalah situs sosial, seperti friendster juga... (Males ngomong nih, tanya ma mbah google aja yah..)
Ya udah, sebelumnya saya posting tentang cara login palsu di friendster, kali ini saya posting tentang cara membuat login palsu di facebook.
Yuuk langsung ke pembahasan...
1. Silahkan anda daftar di http://www.700megs.com
mengapa saya suruh anda daftar disana ?
di web hosting sana sangat gratis dan support php juga dari pada di ripway.com
bila tidak bisa terdaftar langsung saja masuk di :
http://www.700megs.com/register.jsp
2. setelah anda berhasil mendaftar di 700megs.com masuk ke FILE MANAGER...hapus file index.html.(akan ada di Cpanel masing2 nantinya)
3. oke, kita mulai praktek kita.
yang dibutuhkan adalah file index.php dan write.php sebagai inti fakelogin
silahkan download scriptnya dahulu disini atau di
http://www.ziddu.com/download/5023245/scriptFakeloginFacebook.rar.html
ukuran cuma 9kb.
4. setelah anda download. Disana ada dua file sebut saja index dan write
kedua-duanya silahkan anda upload di 700megs.com yang tadi anda sudah daftar.
5. lalu tes terlebih dahulu index.php yg telah kalian upload dan login dari situ,
klo berhasil.. akan ada file baru ;Password.txt [bertujuan sebagai tempat dimana userID dan password yang akan tertampung di facebook fakelogin kamu]
6, alright! selesai sampai di sini. . .
untuk penyebarannya silahkan dengan cara masing2...
disini saya cm kasih contoh satu untuk pengambilan secara paksa account2 facebook mania..
buka file index di www.700megs.com kalian..ambil URL nya.. [penting]
terus untuk pengguna firefox: buka tools>option>main
preview:
disni fungsinya kita mengarahkan agar browser waktu pertama kali dibuka langsung mengarah ke file kita tadi. memungkinkan hasil buruan kalian lebih banyak nantinya.
boleh di sebar ke komputer temen/di warnet2 kesayangan.
atau..
bisa juga menyebarkan dengan cara seperti ini
kamu buat account baru,di yahoo,gmail,ato sejenisnya
dengan nick Facebook@ or something like that.
diatas cm contoh...silahkan kamu buat seni sendiri
enjoy..
mudahkan ??
semoga berhasil . . .
referensi:
forum cyberdos, yogyafree, balikit
dah lama neh ngga corat - coret ups maksudnya tuh ngepost, gw maw cerita neh dikit wktu dolo gw sering dibuat pusing dengan tulisan MSDBGRID32.ocx not found sehingga gw musti kerja 2 kalikok kerja 2 kali? ia soalnya waktu pertama gw bikin program kan pake ADO (Access Data Object) ech gara" ada tulisan kaya gt gw musti ganti ama ADODC (gw lopa kepanjangannya,hehe) tapi sekarang gw ngga ada akan kerja 2 kali lagi karena gw dah dapetin ocx sialannya,hehe. apabila dari kalian" ada kassus sama kaya gw silahkan Download Disini agar ga terjadi error lagi.
duh dah lama y ngga ngepost neh, maklum lah lagi sibuk"nya kul, sampe lopa mpunya blog.hehe yaudah gw ngga akan panjang lebar ngomong di postingan kale ini gw akan membahas tentang Cara Hacking Windows SP2 Artikel ini gw ambil dari artikelnya mas chaidir, mungkin sebagai artikel nya seperti ini
Apakah anda pernah menggunakan komputer di Lab atau pinjam komputer teman atau bahkan menggunakan komputer di tempat umum? Nah, biasanya klo di Lab (berdasarkan pengalaman pribadi) komputer pasti di-password dan jika ingin masuk harus tanya dulu ke sang empunya. Nah, sekarang kita dapat melihat password dari komputer yang kita gunakan tanpa merestart komputer atau pun tanpa menginstall program apapun seperti Cain, L0pthCrack, dsb. Hanya dibutuhkan sedikit ‘kepercayaan’ untuk meminjam komputer (istilah kerennya social engineering) dan 2 buah program, yaitu pwdump6 dan john the ripper. Tapi klo kebetulan ada login umum dengan tipe administrator, itu namanya Hoki! ga perlu cape2 pinjam login teman lagi ![]() .
.
Sebelumnya mungkin anda pernah mendapatkan tutorial mengenai cara menge-hack password user yang ada Windows XP atau NT menggunakan pwdump. Yup, mungkin tutorial ini akan mirip dengan bagaimana cara menge-hack Windows XP, terutama Windows XP SP2. Lalu apa bedanya dengan tutorial yang lain? Saat ini Windows XP SP2 (atau mungkin juga SP1, CMIIW), menggunakan Syskey untuk memproteksi agar HASH (tempat menyimpan password yang dienkripsi) tidak dapat dibaca dan didump menggunakan pwdump atau samdump. Untuk lebih jelasnya berikut penjelasan mengenai Syskey [1] :
Syskey is a Windows feature that adds an additional encryption layer to the password hashes stored in the SAM database. The main purpose of this feature is to deter ‘offline’ attack. In fact one of the most common ways to gather passwords is to copy the system SAM database and then use one of the many good password crackers to “recover” the passwords; of course physical access is almost always required. So with syskey the attacker needs to remove the additional encryption layer to get the password hashes.
Jika dulu mungkin di Windows NT atau XP (sebelum SP2), kita masih bisa menggunakan pwdump atau bahkan langsung dengan KaHT, maka untuk Windows XP SP2 cara tersebut tidak dapat digunakan lagi (mungkin lebih tepatnya, pwdump tersebut tidak dapat digunakan lagi). Nah disinilah letak perbedaan dengan tutorial sebelumnya. Jika sebelumnya kita menggunakan pwdump versi lama, maka sekarang digunakan pwdump6 yang dikembangkan oleh fizzgig and the foofus.net Team. Kalau baca README dari pwdump6 ini, maka pwdump6 adalah :
pwdump6 is a password hash dumper for Windows 2000 and later systems. It is capable of dumping LanMan and NTLM hashes as well as password hash histories. It is based on pwdump3e, and should be stable on XP SP2 and 2K3. If you have had LSASS crash on you using older tools, this should fix that.
A significantly modified version of pwdump3e, this program is able to extract NTLM and LanMan hashes from a Windows target, regardless of whether Syskey is turned on. It is also capable of displaying password histories if they are available. It outputs the data in L0phtcrack-compatible form, and can write to an output file
Oh iya, agar pwdumpd6 dapat dijalankan dan mendapatkan HASH file dibutuhkan account yang mempunyai akses setara dengan Administrator. Nah, oleh karena itu kita harus menjalankan sedikit social engineering. Bilang aja ketemen kita, klo mengakses workgroup, tapi ga bisa klo pake login biasa. Tapi tenang aja, biasanya secara default orang-orang kebanyakan mebuat user dengan tipe account Administrator. Atau gunakan berbagai macam cara, daya, upaya maupun rayuan agar kita bisa dapat login terlebih dulu.
Jika udah punya akses dengan login tipe adiministrator, cara selanjutnya adalah tinggal menjalankan pwdump6. Jika anda punya flashdisk, simpan dan bawa terus pwdump6 ini kemanapun ada pergi, siapa tahu berguna suatu saat.. ![]() . Ok, langsung aja kita jalankan pwdump6 ini. Sebaiknya copy dulu pwdump6 ke Hardisk (jangan dijalankan dari flashdik). Sebelumnya downlod dulu pwdump6 ini dari sini atau download dari mirror situs saya disini.
. Ok, langsung aja kita jalankan pwdump6 ini. Sebaiknya copy dulu pwdump6 ke Hardisk (jangan dijalankan dari flashdik). Sebelumnya downlod dulu pwdump6 ini dari sini atau download dari mirror situs saya disini.
1. Jalankan CMD (Run->cmd)
2. Jalankan pwdump6 seperti berikut (misalnya PwDump6 berada di folder D:\PwDump6)
D:\PwDump6>PwDump.exe -o pass.txt 127.0.0.1
pwdump6 Version 1.3.0 by fizzgig and the mighty group at foofus.net
Copyright 2006 foofus.netThis program is free software under the GNU
General Public License Version 2 (GNU GPL), you can redistribute it and/or
modify it under the terms of the GNU GPL, as published by the Free Software
Foundation. NO WARRANTY, EXPRESSED OR IMPLIED, IS GRANTED WITH THIS
PROGRAM. Please see the COPYING file included with this program
and the GNU GPL for further details.Using pipe {C411BDE9-594E-47F4-99B5-E94ADF194A45}
Key length is 16
Completed.
3. Setelah itu akan didapatkan file pass.txt yang berisi daftar user dan password yang masih dienkripsi. Contohnya akan tampak seperti berikut :
ach:1003:2BFA42D08601B951ABD697149E2F5967:73098347042E9109FA584CE843018F4F:::
Administrator:500:934A4750EC9859B3EA397B0F6EC18E34:732BD09D6834DA4A5A30300A6A045BF8:::
coba:1004:FBE4F28EE205F0BA79999C25263AA9AA:A69C199A4DF77CD41FCA6EA916A93868:::
Guest:501:NO PASSWORD********************* :NO PASSWORD*********************:::
HelpAssistant:1000:B3D2AE56C93F27B43C4F8419B1A21E9B: DC3DBB258A10B0C7EA9D92133267B905:::
SUPPORT_388945a0:1002:NO PASSWORD*********************: DF1DB672DA1B5C045ECA2490CA753D3B:::
4. Yosh!! password sudah ditangan. Proses selanjutnya adalah menge-crack file pass.txt dengan bantuan John The Ripper. Sebaiknya simpan dulu file pass.txt ke USB atau upload ke tempat yang aman, karena proses cracking ini bisa dilakukan kapan saja dan dimana saja. Berdasarkan pengalaman, kalau passwordnya tidak terlalu sulit ditebak seperti “adminkeren”, “qwerty123″, biasanya dibutuhkan waktu yang tidak terlalu lama untuk mengecracknya lewat John The Ripper. Tapi kalau password menggunakan kombinasi yang aneh-aneh seperti “P4ssW0rD”, “S03S4h”, dsb, biasanya membutuhkan waktu lama, bisa ditinggal tidur atau maen aja dulu. Ok, sekarang gini nih cara ngecraknya.
Download John The Ripper untuk Windows disini. Untuk komputer yang menggunakan Prosesor AMD, sebaiknya menggunakan “john-mmx.exe”. Atau bagi yang menggunakan intel atau AMD, dapat menggunakan “John-386.exe”. Sebelumnya copy file pass.txt ke dalam folder tempat “John-mmx.exe” atau “John-386.exe” berada (John171w\john1701\run). Setelah itu tinggal jalankan perintah berikut dan tunggu dengan sabar :
D:\john171w\john1701\run>john-mmx.exe pass.txt
Loaded 8 password hashes with no different salts (NT LM DES [64/64 BS MMX])
REN123 (Administrator:2)
TEBAK (coba:2)
ADMINKE (Administrator:1)
MUDAHDI (coba:1)
Yosh!! sekarang passwordnya sudah terlihat secara kasat mata. Jadi password untuk user “Administrator” adalah “adminkeren123″, diperoleh dari menggabungkan Administrator:2 dan Administrator:2.
Administrator:1+Administrator:2 = adminkeren123
Sedangkan untuk user “coba” adalah “mudahditebak”!!
Mudah bukan? Intinya sih tinggal ambil HASH file (password yang dienkripsi) menggunakan pwdump6 lalu crack hasilnya dengan John The Ripper.
Nah, sekarang kalau kita mau pakai komputer teman di Lab, ga usah cari2 orangnnya lagi. Tinggal pake aja langsung user Admin lagi, tapi jangan sampai ketahuan ama dia….. ![]() Atau klo anda lupa password Administrator, tidak perlu mereboot komputer, lalu mereset password anda. Tinggal ikut langkah2 diatas aja!
Atau klo anda lupa password Administrator, tidak perlu mereboot komputer, lalu mereset password anda. Tinggal ikut langkah2 diatas aja!
Referensi :
[1]. http://studenti.unina.it/~ncuomo/syskey
Thanks to fizzgig for you great tools, pwdump6 (http://www.foofus.net/fizzgig/pwdump)! I’ve been looking for this tools for a log time ago! Thanks dude!! and Thanks to pen-test@securityfocus.com!
Sumber : Klik












585.photobucket.com/albums/ss296/batlax150/danywebsite.png)

